IEC 62443 es el estándar internacional para cybersecurity en sistemas de control industrial (ICS). Crítico para plantas, utilities, infrastructure. Parallels ISO 27001 for IT pero adaptado a OT specificities: safety, realtime, legacy equipment. Con NIS2 push, empresas con OT must master this. Este artículo IT-team-friendly overview.
Por qué IT teams deben conocer
- Convergencia IT/OT: líneas borrosas.
- NIS2 obliga a muchas empresas integrar OT security.
- Coordinación: IT ciberseguridad debe alinear con OT.
- Audit: IT teams auditan OT increasingly.
IEC 62443 structure
Series de standards:
- 62443-1-x: general (terminology, concepts).
- 62443-2-x: policies y procedures.
- 62443-3-x: system requirements.
- 62443-4-x: component requirements.
Comprehensive.
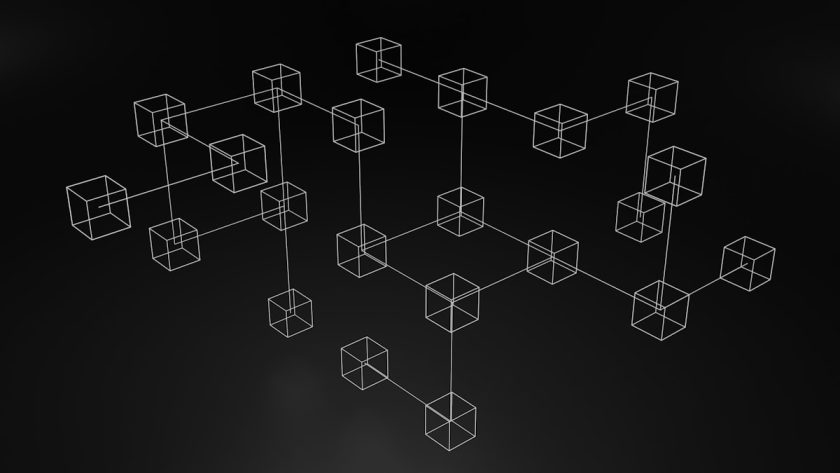
Zones y conduits
Core concept: segmentar networks en zones, connect via conduits:
- Zone: group de assets con similar security requirements.
- Conduit: network path between zones con defined security.
- Trust boundaries: explicit.
Similar IT DMZ pero formalized.
Purdue Model
Reference architecture:
- Level 0: sensors, actuators.
- Level 1: PLCs, RTUs.
- Level 2: SCADA, HMI.
- Level 3: manufacturing operations (MES).
- Level 3.5: DMZ.
- Level 4-5: enterprise IT.
IEC 62443 incorporates Purdue conceptualmente.
Security Levels (SL)
62443 defines 4 SLs:
- SL 1: protection casual/inadvertent.
- SL 2: intentional with simple means.
- SL 3: intentional with sophisticated means.
- SL 4: intentional sophisticated + extensive resources.
Assess zone SL target, implement controls matching.
Roles
Framework distinguishes:
- Asset owner: operates system.
- System integrator: builds.
- Product supplier: makes components.
Each has distinct obligations. Clear separation of responsibility.
Foundational Requirements
7 foundational requirements (FRs):
- Identification and Authentication Control (IAC).
- Use Control (UC).
- System Integrity (SI).
- Data Confidentiality (DC).
- Restricted Data Flow (RDF).
- Timely Response to Events (TRE).
- Resource Availability (RA).
Basis de all assessments.
Security Program (CSMS)
Cybersecurity Management System (CSMS):
- Risk assessment.
- Security program definition.
- Implementation.
- Maintenance.
- Improvement.
Similar ISO 27001 ISMS pero OT-focused.
Certification
Available certifications:
- IEC 62443-2-4: system integrator.
- IEC 62443-3-3: system.
- IEC 62443-4-1: secure development lifecycle.
- IEC 62443-4-2: component.
Industry demands increasingly.
vs ISO 27001
Comparative:
| Aspect | IEC 62443 | ISO 27001 |
|---|---|---|
| Focus | OT / industrial | IT / info security |
| Safety | Critical | Not primary |
| Legacy equipment | Handles | Less |
| Realtime | Considered | No |
| Certifications | Multiple | ISMS |
| Complementary | Yes | Yes |
Use both: ISO 27001 enterprise, 62443 OT zones.
NIS2 alignment
NIS2 mandates OT security. 62443:
- Recognized framework.
- Evidence compliance con NIS2.
- Risk management: 62443 provides methodology.
Adoption 62443 accelerates NIS2 compliance.
IT-OT coordination
Where IT teams help OT:
- Network segmentation via VLANs, firewalls.
- Monitoring: SIEM ingests OT logs.
- Incident response procedures alignment.
- Patch management: different cadence pero coordinated.
- Identity management: across domains.
Where IT doesn’t: don’t change OT without understanding impact.
Common IT mistakes
- Patch aggressively: OT patches require coordination con safety.
- Rolling updates: OT systems may require specific windows.
- IT-grade crypto: OT may need lighter (realtime constraints).
- “IT best practices” blindly applied: may break OT.
Respect OT expertise.
Technologies relevant
- Industrial firewalls: Moxa, Hirschmann.
- Data diodes: unidirectional for critical.
- Industrial IDS: Claroty, Nozomi, Dragos.
- SIEM OT integration: Splunk, QRadar OT modules.
- OT patch management: specialized tools.
Specific tech stack.
Implementation phases
Typical org journey:
- Asset inventory OT (often poor).
- Zone/conduit diagram.
- Risk assessment.
- Gap analysis vs 62443.
- Control implementation priorities.
- Continuous improvement.
Years-long typically.
Budget considerations
- Consultancy: expert analysis.
- Tech stack: firewalls, IDS, monitoring.
- Training: OT + IT cross-pollination.
- Certification: if pursued.
Significant but justified vs incident cost.
Recent updates
- IEC 62443-2-1: 2024 update.
- Cloud OT: emerging considerations.
- Wireless: 5G private integration.
- Remote access: vendor access management.
Standard evolving.
Integration con other frameworks
- NIST CSF: complementary, US-centric.
- ISO 27001: ISMS layer.
- NERC CIP: North American utility.
- CIS Controls: tactical guidance.
Most enterprises mix.
Conclusión
IEC 62443 is serious framework for OT cybersecurity. Para IT teams in empresas con industrial operations, understanding essential. Convergence IT/OT + NIS2 push force this. Not “adopt everything overnight” — years-long gradual journey. IT teams contribuye: segmentation, monitoring, incident response. OT teams own: actual OT operations, specific controls. Coordination matters. Con attacks industrial increasing (Colonial Pipeline, Oldsmar, others), this no es theoretical — urgente.
Síguenos en jacar.es para más sobre IEC 62443, OT security y NIS2.